Cryptography 101
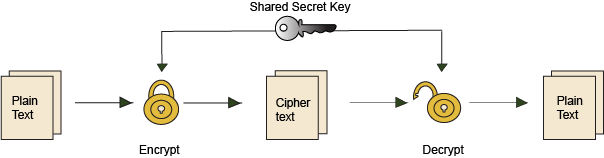
Traditional cryptography uses the same key to encrypt information as it uses to decrypt information. As a result, it requires that the keys used for encryption and decryption be kept secret. This kind of cryptography is not appropriate for a document that needs to be authenticated by many, diverse systems.
ePassports use asymmetric cryptography. This means that two different keys are used: one key to encrypt, and another key to decrypt. The key used to encrypt the data is kept extremely secure and is known as the “private key”. The other key, called the “public key” is widely distributed and can be used to decrypt the data. Together, these two keys are known as a “key pair”.
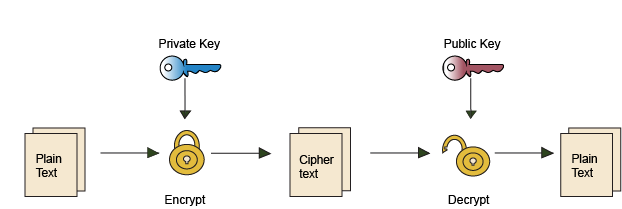
This asymmetric encryption method is used to create the digital signature found in ePassports. For ePassports, the purpose of encrypting the information is not to keep it secret. After all, the information can be easily read on the data page of the ePassport. The process of encrypting and decrypting is designed to detect if the data stored on the chip has been modified and to confirm the authenticity of the data. Decrypting achieves this because nobody but the issuing State could have encrypted the information using their private keys. In addition to confirming authenticity, the process of verifying the digital signature can also detect tampering. If even one character is changed in the information stored on the chip, the verification of the digital signature will fail.
Trust Chain
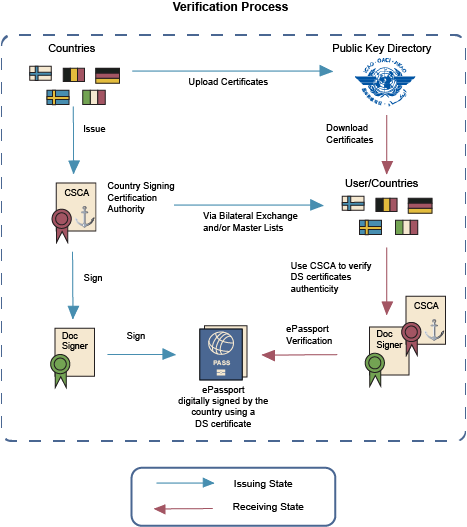
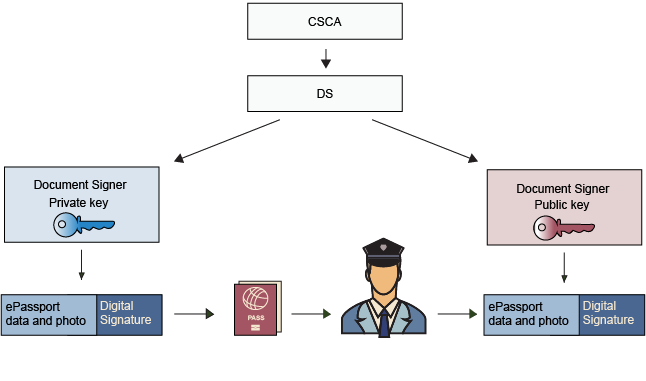
In the context of ePassports, each Issuing State has at least two types of key pairs. A
Country Signing Certification Authority (CSCA) key pair and a Document Signer Certificate (DSC) key pair. When issuing an ePassport, the CSCA private key digitally signs the DS Certificate. The DS private key digitally signs the ePassport.
Figure 1: The chain of trust

A digital signature on an ePassport is derived from the issuing State’s security certificates, each of which contains the public key that can be used to verify its authenticity—the Country Signing Certification Authority (CSCA) Certificate and the Document Signer Certificate (DSC). Together, the signature and certificates form a trust chain wherein one end is securely anchored in the authority of the issuing State and the other end is securely stored in the chip of the ePassport as the Document Security Object. The Document signer must be validated against the CSCA to validate the digital signature to complete the whole chain of trust regarding the signatures.
When conducting ePassport validation, passive authentication is the process of validating the authenticity and integrity of the content of the chip of an ePassport by verifying the digital signature on the document using the public keys of the issuing State. When the appropriate infrastructure and systems are in place, this process informs border authorities that the electronically stored information in the ePassport is authentic, was issued by the given country and has not been tampered with.